Digital Forensics &
Incident Response (DFIR)
When a breach occurs, your response dictates your legal liability and operational survival.
We deploy intelligence-led incident responders to contain adversaries, preserve forensic evidence for your insurance carrier, and securely rebuild your enterprise infrastructure.
"The perimeter has been breached."
What you do next determines whether your business survives. Do not reboot your servers. Do not format your hard drives. You need an intelligence-led strategy to preserve the evidence and systematically eradicate the adversary.
The Danger of a Botched Response
The worst damage from a cyberattack rarely comes from the initial breach; it comes from an inexperienced internal IT team making panicked decisions during the aftermath.
Here is the operational and legal friction our DFIR practice eliminates.
Methodical Recovery. Defensible Forensics.
We don’t guess, and we don't act on panic.
We follow a strict, intelligence-community framework to neutralize the adversary, minimize your downtime, and establish a legally defensible chain of custody.
Order out of Chaos
Identity control is not enough if your endpoint can still execute malware. Our unique Zero Trust methodology blends Microsoft Identity with Application execution control for ultimate resilience.
Strategic Rebuilding
We do not just investigate the breach; we are enterprise cloud architects. Once the threat is neutralized, we immediately rebuild your infrastructure to a modern, zero-trust standard so this never happens again.
Cyber Insurance Alignment
We speak the language of insurance carriers and breach coaches. Our strict adherence to forensic chain-of-custody protocols ensures your claim isn't denied due to spoliation of evidence.
Elite Adversarial Tradecraft
You are fighting organized crime; you need responders who understand their tactics. Our analysts use intelligence-grade tools to outmaneuver the adversary and secure your perimeter.
Defensible Legal Posture
Our final reports are built for the boardroom and the courtroom. We give your legal counsel the definitive, factual clarity they need to navigate regulatory disclosures without assuming unnecessary liability.
Do Not Trust Your Local MSP
to Investigate a Breach
Standard IT providers are built to maintain networks, not investigate advanced persistent threats.
When an MSP encounters a breach, their instinct is often to blindly format servers or restore from backups immediately. This destroys the evidence, violates your cyber insurance policy, and leaves the original vulnerability wide open.
Cloudskope’s DFIR practice consists of incident commanders, forensic analysts, and former U.S. Intelligence operators. We bring a structured, methodical response to your crisis. We take command of the incident, legally preserve the digital crime scene, and systematically hunt the adversary out of your network before rebuilding your infrastructure.
When to Engage DFIR
Do not wait for a full network collapse.
Contact Cloudskope immediately if you experience any of the following critical indicators of compromise.

Post-Ransomware Recovery
Files have been encrypted and operations are halted. You need an elite team to assess the damage, clear the environment, and securely restore operations.
Business Email Compromise (BEC)
You discover unauthorized forwarding rules in Microsoft 365, or a client reports wiring money to a fraudulent account based on an email from your executive team.
The FBI/CISA Notification
You receive a formal notification from federal law enforcement or your cloud provider informing you that your network is communicating with known malicious infrastructure.
Proactive Executive Readiness
ou want to prepare your leadership team before a disaster strikes by building a formal Incident Response Plan and executing a simulated Tabletop Exercise.
The Supply Chain Compromise
A critical third-party software vendor or your current Managed Service Provider (MSP) was just breached.
You need an immediate, independent compromise assessment to prove to your board, clients, and insurance carrier that the adversary did not pivot into your internal infrastructure.
The Malicious Insider
You suspect a departing executive, a disgruntled IT administrator, or a highly privileged user is actively exfiltrating corporate data or sabotaging systems.
You need a covert, legally defensible forensic investigation to lock them out and secure the evidence before the damage becomes permanent.
Frequently Asked Questions
Answers to the most common questions about scope, process, and what happens after the audit.
Disconnect affected machines from the network (pull the ethernet cable or disable Wi-Fi), but do not turn off the power. Turning off the power destroys the volatile memory we need to investigate the attack. Contact our team to initiate an incident scoping call.
Yes. We frequently partner with breach coaches, outside legal counsel, and cyber insurance carriers. Our forensic procedures strictly align with industry standards to ensure evidence is preserved and your claim remains valid.
We strongly advise against paying ransoms. Paying does not guarantee data recovery and funds organized crime. Our primary goal is to determine the scope of the breach, eradicate the threat, and restore your operations safely from backups.
Yes, this is our core differentiator. While some forensic firms simply hand you a report and leave, Cloudskope is a full-stack engineering firm. We transition seamlessly from forensic investigation into a complete architectural rebuild, deploying Zero Trust controls to prevent a secondary attack.
Absolutely. We develop comprehensive Incident Response Plans (IRPs), conduct executive tabletop exercises, and run active compromise assessments to ensure your baseline is secure and your team knows exactly how to respond.
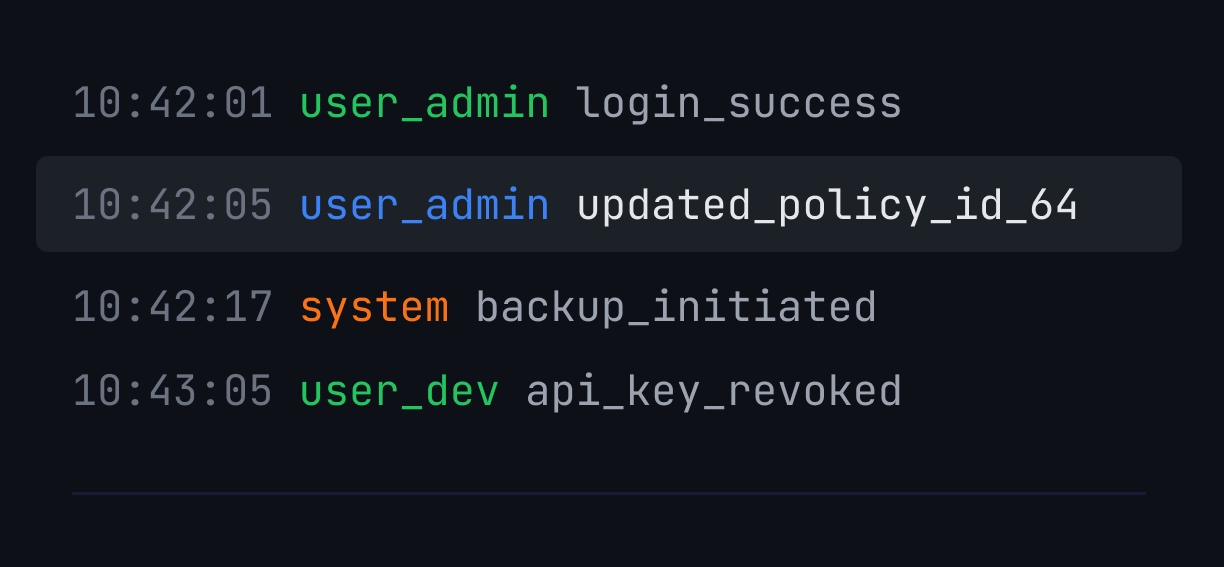
Digital forensics and incident response (DFIR) is a specialized discipline that combines the science of forensic investigation with the operational practice of containing and eradicating cyberattacks. Digital forensics involves capturing and preserving evidence from compromised systems — memory dumps, log files, network telemetry, and disk images — to determine exactly what happened, how the attacker got in, and what data was accessed. Incident response is the tactical operation of stopping the attack, removing the adversary, and restoring operations securely. Together, DFIR gives organizations the factual record required by legal counsel, regulators, and cyber insurance carriers — while getting the business back online as fast as possible.
Yes. We frequently parachute in to work alongside—or take command from—existing internal IT teams and local MSPs. We bring the specialized adversarial tradecraft and forensic expertise that standard IT providers simply do not possess.
Wiping servers destroys the digital crime scene. Without a forensic investigation, you cannot prove what data was stolen (creating a massive regulatory liability), you violate your cyber insurance policy's chain-of-custody rules, and you leave the original backdoor wide open for the attacker to return.
Do Not Face the Adversary Alone
Handling a cyberattack requires elite tradecraft, legal precision, and methodical operational control. Stop guessing and stop destroying the evidence.
Let Cloudskope’s DFIR commanders investigate the breach, eradicate the adversary, and bring your business safely back online.
.png)
