30 Biggest Data Breaches of All Time: A Ranked Analysis of Impact, Cost, and Regulatory Precedent

<p>Listing breaches by record count alone produces a misleading ranking. The Yahoo 2013 disclosure compromised 3 billion accounts; the SolarWinds Orion compromise affected approximately 18,000 organizations and a few hundred meaningful targets within them. By records, Yahoo is twenty thousand times larger. By geopolitical and regulatory consequence, SolarWinds may be the more important event. This ranking weights five dimensions — records exposed, financial and regulatory cost, strategic and intelligence significance, downstream regulatory precedent, and the durability of the systems and controls that the breach forced into existence — to produce the list of incidents that matter most for executives, boards, and private equity sponsors.</p>
Methodology
Each breach is evaluated across five dimensions, scored qualitatively, and combined into a composite rank. The dimensions are:
- Records exposed — the raw count of affected individuals or accounts. Useful but not determinative; some 50-million-record breaches produced larger regulatory consequence than some 500-million-record breaches.
- Direct financial and regulatory cost — the total of regulatory penalties, civil settlements, remediation expenses, and ongoing compliance costs.
- Strategic and intelligence significance — the geopolitical, defense, and national-security implications, including attribution to state-sponsored actors and the operational uses of the exfiltrated data.
- Regulatory precedent and durability — the extent to which the breach catalyzed regulatory frameworks, enforcement standards, or industry practices that persist.
- Architectural consequence — the extent to which the breach drove changes in security architecture, software supply chain practice, or M&A diligence standards.
Rankings are anchored against the Cloudskope Breach Library, where deep analysis of each incident is available.
1. Yahoo 2013-2014
3 billion accounts (2013) + 500 million (2014). $500M+ direct cost. FSB attribution. The largest data breach in history by record count and the foundational SEC enforcement precedent for treating undisclosed cybersecurity incidents as material securities violations. The $35M Altaba settlement directly informed the 2023 SEC Cybersecurity Disclosure Rules. The $350M Verizon acquisition price reduction was the first major cyber-driven M&A repricing. Marissa Mayer's forfeit of approximately $14M in compensation and General Counsel Ron Bell's resignation without severance established the executive-accountability precedent that every subsequent major incident response has navigated. Read the full analysis.
2. Equifax 2017
147 million U.S. consumers. $1.4B+ direct cost. The credit reporting agency's failure to patch a known Apache Struts vulnerability (CVE-2017-5638) exposed Social Security numbers, dates of birth, addresses, and driver's license numbers for nearly half the U.S. adult population. The $1.4 billion-plus in settlements with the FTC, CFPB, state attorneys general, and consumer class actions established the modern penalty calibration for breaches of regulated financial data. The CFPB's continuing oversight role made Equifax the foundational case for sectoral financial regulator enforcement of cybersecurity, parallel to the FTC's consumer-protection track. CEO Richard Smith's resignation and the criminal insider-trading charges against three executives extended individual accountability beyond civil compensation forfeiture.
3. Marriott-Starwood 2018
344 million guests globally across three breaches. $170M+ direct cost. Chinese state-sponsored attribution. The canonical M&A cyber inheritance case. Chinese attackers were inside Starwood's reservation database for two years before Marriott's $13.6 billion 2016 acquisition closed and for two more years after. The October 2024 FTC consent order — running 20 years through 2044 with prescriptive zero trust architecture requirements — is the most operational cybersecurity enforcement order the FTC has issued. The case reshaped cyber due diligence practice: forensic threat hunting is now standard, not premium. Read the full analysis.
4. Facebook / Cambridge Analytica 2018
87 million profiles. $5.7B+ direct cost. The $5 billion FTC settlement in July 2019 was the largest consumer-protection penalty in U.S. history at the time of imposition. The case established that consent-based data exposure — data collected through legitimate API access but used outside the scope users could understand — is a regulatory category equivalent to technical breach. Cambridge Analytica accelerated GDPR's enforcement posture, catalyzed the California Consumer Privacy Act and its state-law successors, and produced the named-officer certification framework that subsequent FTC enforcement actions have replicated. Read the full analysis.
5. SolarWinds Orion Supply Chain Compromise 2020
18,000+ organizations notified; ~100 high-value targets confirmed. Attribution to Russian SVR (APT29 / Cozy Bear). The Russian SVR compromised SolarWinds' Orion update infrastructure, embedded malicious code (SUNBURST) in software updates distributed to thousands of customers including U.S. federal agencies, and operated inside selected targets for months. The breach reset U.S. government and private-sector software supply chain practice; the May 2021 Executive Order 14028 ("Improving the Nation's Cybersecurity") was substantially driven by the SolarWinds facts. The October 2023 SEC enforcement action against SolarWinds and CISO Timothy Brown was the first SEC personal-liability action against a sitting CISO. Read about the SEC enforcement.
6. T-Mobile 2021
76 million customers. $350M class action settlement + $15.75M FCC settlement. The August 2021 breach exposed names, dates of birth, Social Security numbers, driver's license numbers, and IMEI/IMSI device identifiers — the most consequential exposure of telecom subscriber data in U.S. history. The FCC settlement was the first major FCC consent decree treating cybersecurity practice as a regulated telecommunications matter. The case is the canonical example of the carrier-industry threat landscape and the regulatory precedent for telecommunications-specific cybersecurity expectations.
7. Anthem 2015
78.8 million records. $115M class action settlement + $39.5M state AG settlement + $16M HHS settlement. Chinese state-sponsored attackers compromised health-insurance records for nearly 80 million Americans — names, dates of birth, Social Security numbers, employment information, and medical identifiers. The breach is operationally consistent with the Chinese intelligence pattern of building consolidated biographical databases on U.S. persons of intelligence interest. The case established health-insurance industry cybersecurity expectations under HIPAA's Security Rule and prompted the HHS Office for Civil Rights to substantially increase its enforcement posture.
8. Office of Personnel Management (OPM) 2015
22.1 million federal employee and contractor records. Chinese state-sponsored attackers compromised the security clearance background investigation records of approximately 22 million current and former U.S. federal employees, contractors, and their relatives — including the SF-86 forms containing extensive biographical, financial, and personal information used in security clearance adjudication. The breach is the largest disclosed compromise of U.S. government personnel records and is the foundational case for understanding the strategic intelligence value of consolidated biographical databases. Director Katherine Archuleta resigned. The breach catalyzed substantial reorganization of federal cybersecurity, including the eventual establishment of CISA.
9. Capital One 2019
106 million customers in the U.S. and Canada. $80M OCC penalty + $190M class action settlement. A former AWS employee exploited a misconfigured web application firewall to access Capital One's S3 buckets and exfiltrate consumer credit application data. The OCC's $80 million penalty was the first major sectoral financial regulator enforcement of cybersecurity practice at a bank, parallel to and informed by the post-Equifax CFPB framework. The case is the canonical cloud-misconfiguration breach and the foundational example of cloud security as a regulated banking concern.
10. Target 2013
110 million customers (40M payment cards + 70M PII). $290M+ direct cost. Holiday-season attackers used credentials stolen from a third-party HVAC vendor to penetrate Target's network and deploy memory-scraping malware on point-of-sale systems. The breach is the foundational vendor-risk-management case study and the first major retail breach to produce material executive consequences — CEO Gregg Steinhafel's resignation in May 2014 was the first CEO departure directly attributed to a cybersecurity incident at a major U.S. retailer. The case substantially accelerated the U.S. transition from magnetic-stripe to EMV chip payment cards.
<p>The right framework for ranking breaches is not records exposed but durable regulatory and operational consequence. By that standard, Yahoo, Equifax, SolarWinds, Cambridge Analytica, and Marriott-Starwood are the five breaches that built modern cybersecurity governance.</p>
11. JP Morgan Chase 2014
76 million households + 7 million small businesses. Attackers compromised JPMorgan's network through credentials stolen from an employee, exfiltrating names, addresses, phone numbers, and email addresses but not (per JPMorgan's representation) financial account data. The breach is the foundational financial-sector cybersecurity case and the precedent for the kind of large-bank breach disclosure that subsequently informed sectoral regulator enforcement. Three Israeli-Russian hackers were ultimately indicted; the operation was the largest financial-sector breach disclosed at the time. Read the full analysis.
12. Home Depot 2014
56 million payment cards + 53 million email addresses. $200M+ direct cost. Attackers used credentials stolen from a third-party vendor (similar to the Target pattern) to compromise Home Depot's point-of-sale systems. The breach was disclosed approximately ten months after Target's, demonstrating that retail-industry vendor-risk-management practice had not yet adapted to the post-Target threat landscape.
13. Uber 2016
57 million riders and drivers. $148M state AG settlement. Attackers obtained credentials from a private GitHub repository, used them to access Uber's AWS environment, and exfiltrated rider and driver data. Uber paid the attackers $100,000 through its bug bounty program in an attempt to suppress disclosure — a fact that surfaced in November 2017 and produced the $148 million state attorney general settlement plus the criminal conviction of CSO Joseph Sullivan in 2022 for obstruction of justice and misprision of a felony. Sullivan's case is the first criminal conviction of a sitting Chief Security Officer for breach-response conduct.
14. eBay 2014
145 million customers. Attackers used credentials stolen from a small number of eBay employees to access a corporate database containing customer names, encrypted passwords, email addresses, physical addresses, phone numbers, and dates of birth. The breach is one of the largest by record count and is a foundational case for understanding employee credential compromise as a primary attack vector for major platforms.
15. Adult Friend Finder 2016
412 million accounts across multiple sites. Attackers compromised FriendFinder Networks and exfiltrated the user databases of Adult Friend Finder, Penthouse, Cams.com, and related sites. The exposure included usernames, email addresses, and unsalted SHA-1-hashed passwords — cryptographically inadequate by 2016 standards and trivially crackable on commodity hardware. The breach is one of the largest by record count and is a reference case for the consumer-harm consequences of sensitive-data exposure beyond financial information.
16. MySpace (disclosed 2016, breach 2008)
360 million accounts. The 2008 MySpace breach surfaced in 2016 when the user database appeared for sale on dark web marketplaces. The exposed passwords were stored under SHA-1 with no salting — standard practice at the time but cryptographically inadequate even then. The breach is foundational for understanding the long tail of legacy-system data exposure: data collected before modern security standards persists indefinitely and may surface years or decades after the underlying compromise.
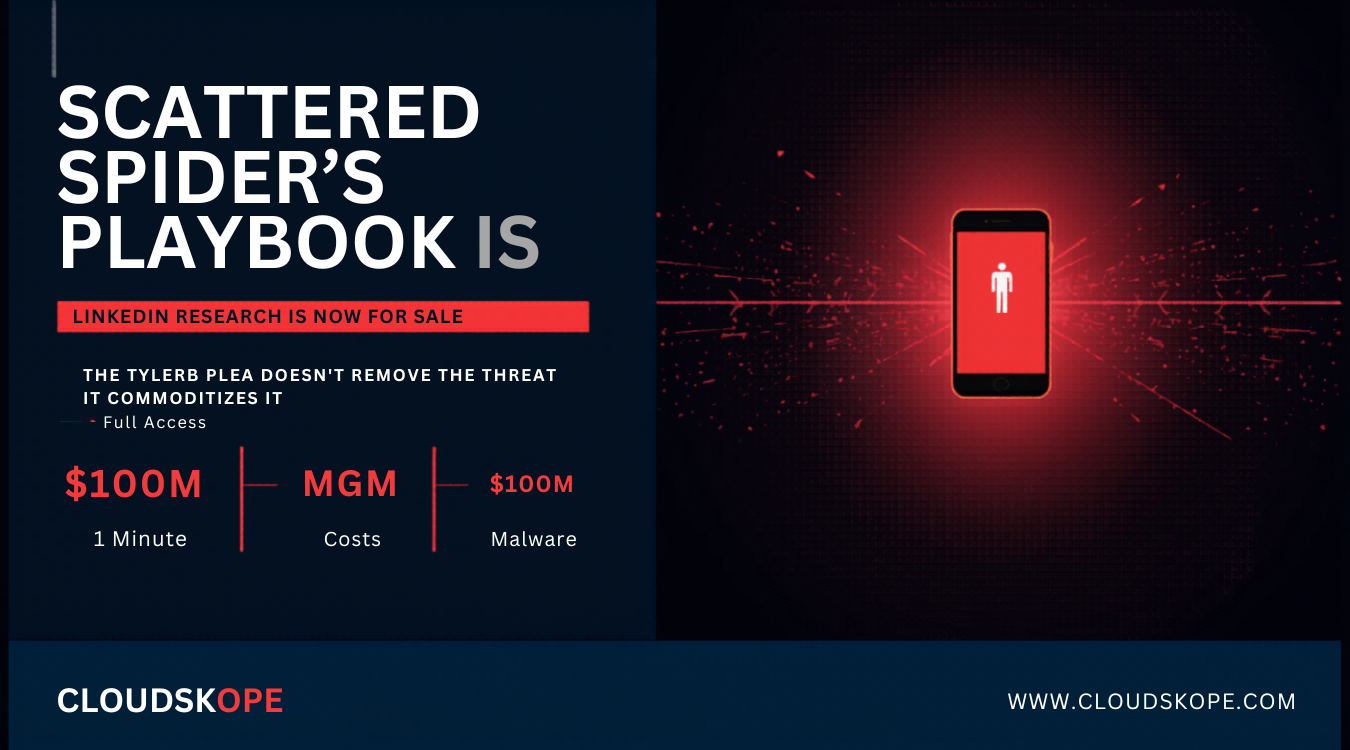
17. LinkedIn 2012 (disclosed 2016) and 2021 scrape
165 million accounts (2012) + 700 million scraped profiles (2021). The 2012 LinkedIn breach exfiltrated approximately 165 million user credentials stored under SHA-1 without salt. The credentials surfaced in dark web marketplaces in 2016 and have informed credential-stuffing attacks across the platform ecosystem for nearly a decade. The separate 2021 "scrape" of approximately 700 million LinkedIn profiles — collected through automated public-profile harvesting rather than unauthorized access — is technically not a breach but is operationally consequential for downstream identity-fraud and targeted-attack workflows.
18. Adobe 2013
153 million accounts. Attackers compromised Adobe's source-code repository and customer database, exfiltrating user names, encrypted credit card information, and encrypted passwords (with password hints stored in plaintext). The plaintext password hints were the consequential exposure: combined with the encrypted passwords, the hints enabled substantial password recovery and informed credential-stuffing attacks against other platforms. The breach is foundational for understanding cryptographic inadequacy in password storage at scale.
19. MOVEit / Clop 2023
95+ million records across 600+ organizations. The Clop ransomware group exploited a zero-day SQL injection vulnerability (CVE-2023-34362) in Progress Software's MOVEit Transfer file-transfer product to compromise more than 600 organizations using the product, including major U.S. federal agencies, state governments, universities, financial services firms, and healthcare organizations. The campaign is the largest single supply-chain compromise by victim count and is the foundational case for understanding third-party file-transfer software as a high-value target category. Read the related GoAnywhere MFT analysis, which preceded MOVEit by months and established the pattern.
20. Change Healthcare 2024
~190 million Americans. $872M Optum-reported costs. Attackers compromised Change Healthcare — the subsidiary of UnitedHealth Group that processes approximately 14 billion healthcare claims annually — and exfiltrated protected health information for roughly 190 million Americans, more than half the U.S. population. The operational disruption to U.S. healthcare claims processing extended for weeks and produced cascading impacts on hospital cash flow, pharmacy operations, and patient care. UnitedHealth CEO Andrew Witty's congressional testimony confirmed that Change Healthcare paid a $22 million ransom to the BlackCat / ALPHV ransomware affiliate. The breach is the largest healthcare-sector breach in U.S. history.
21. Snowflake / Ticketmaster 2024
560 million Ticketmaster records + customer impact across multiple Snowflake tenants. Attackers using infostealer-harvested credentials accessed multiple Snowflake customer tenants that lacked multi-factor authentication on the affected accounts. The compromise affected Ticketmaster (560M records), AT&T (73M customers), Santander Bank, and other Snowflake customers. The campaign is foundational for understanding the credential-stuffing attack surface created by cloud data warehouse customer-managed access controls, and for the regulatory framing around shared-responsibility security in cloud SaaS.
22. AT&T 2024
73 million current and former customers. AT&T disclosed in March 2024 that approximately 73 million customer records — including Social Security numbers, account information, and dates of birth — had been leaked on dark web marketplaces. A separate July 2024 disclosure addressed the compromise of approximately 109 million customer call and text records through AT&T's Snowflake tenant. The combined AT&T disclosures illustrate the multiple-vector exposure that large enterprises face in cloud-era operations.
23. Microsoft Exchange ProxyLogon 2021
250,000+ organizations compromised globally. Chinese state-sponsored actor HAFNIUM exploited four zero-day vulnerabilities in Microsoft Exchange Server (CVE-2021-26855, -26857, -26858, -27065) to deploy web shells on hundreds of thousands of Exchange servers globally. The campaign was so extensive that the FBI executed a court-authorized operation in April 2021 to remove web shells from affected servers without owner consent — the first such operation in U.S. cybersecurity enforcement history. ProxyLogon catalyzed the broader migration from on-premises Exchange to Microsoft 365, and substantially accelerated CISA's role as operational coordinator of national cybersecurity response.
24. Colonial Pipeline 2021
5,500 miles of pipeline shut down. $4.4M ransom paid (subsequently partially recovered by FBI). The DarkSide ransomware group compromised Colonial Pipeline's billing systems through a compromised VPN account lacking multi-factor authentication. Colonial proactively shut down pipeline operations to contain the incident, producing fuel shortages across the U.S. southeast. The case is the foundational ransomware-as-critical-infrastructure-threat precedent and substantially informed the May 2021 TSA pipeline cybersecurity directives and the broader CISA critical infrastructure cybersecurity framework.
25. Kaseya VSA 2021
~1,500 downstream organizations affected via MSP supply chain. $70M ransom demand. The REvil ransomware group exploited a zero-day vulnerability in Kaseya's VSA remote management software to deploy ransomware through managed service providers (MSPs) to approximately 1,500 downstream organizations. The campaign is the canonical MSP-supply-chain ransomware case and is foundational for understanding the asymmetric attack surface created by MSP-level access to many downstream networks.
26. Canvas / Instructure 2026
275 million users. 8,809 schools affected. EdTech vendor disclosure failure. The May 2026 compromise of Canvas / Instructure exposed records for hundreds of millions of students and educators globally and disrupted operations at thousands of schools and universities. The case is the foundational EdTech-vendor accountability incident under FERPA and parallel state student-privacy frameworks. Read the full analysis.
27. Bybit 2025
$1.4 billion in cryptocurrency stolen. The February 2025 compromise of Bybit's Ethereum cold wallet — attributed to North Korean state-sponsored actor Lazarus Group — is the largest single cryptocurrency theft in history. The case is foundational for understanding the operational sophistication of DPRK state-sponsored cryptocurrency theft as a sovereign revenue source and for the FATF-track international response to crypto-laundering networks. Read the full analysis.
28. Microsoft 365 Token Theft Campaign 2026
Targeted state-sponsored campaign affecting U.S. government and Fortune 500 enterprises. The 2026 campaign exploited weaknesses in Microsoft Entra ID token issuance and validation to enable persistent unauthorized access to Microsoft 365 tenants across U.S. federal agencies and major enterprises. The case is operationally significant for understanding cloud identity infrastructure as a single-point-of-failure for organizations dependent on Microsoft 365. Read the full analysis.
29. Adobe 2024-2026 incidents
Multiple platform compromises. The 2024-2026 series of Adobe Creative Cloud and adjacent platform compromises is the foundational case for SaaS-platform-as-attack-vector in creative and marketing technology stacks. Read the full analysis.
30. Stryker Cyberattack 2026
Medical device manufacturer breach with continuity implications. The 2026 Stryker cyberattack is the foundational medical-device-manufacturer cybersecurity case and is operationally significant for understanding the continuity-of-care implications of cybersecurity incidents at companies that supply critical medical infrastructure. Read the full analysis.
Themes that emerge across the 30
State-sponsored attribution dominates the top tier. Of the top 10 by composite impact, six (Yahoo, Marriott-Starwood, SolarWinds, Anthem, OPM, Microsoft Exchange ProxyLogon) are attributed to state-sponsored actors. The implication for executives is that the threat model for major consumer-data-rich and critical-infrastructure organizations must include state-sponsored intelligence collection as a primary scenario, not an edge case.
The detection-delay pattern is consistent. Across the top 10, detection delays of 2-4 years between initial compromise and disclosure are standard, not exceptional. The operational implication is that current threat-hunting practice must look for compromises that may already be 24+ months old, not just for fresh intrusions.
Third-party and supply-chain vectors are increasingly central. SolarWinds, MOVEit, Kaseya, Snowflake-related compromises, Microsoft Exchange ProxyLogon, and Change Healthcare all involved third-party-software or shared-platform vectors. The implication for executives is that vendor risk management is no longer an adjunct security function but a primary one.
Regulatory consequence is increasingly individualized. The Yahoo executive forfeiture, the Equifax executive insider-trading prosecutions, the Uber CSO criminal conviction, the SolarWinds CISO SEC enforcement, and the Facebook named-officer certification requirements collectively indicate that future major incidents will produce personal accountability for sitting officers, not just corporate civil liability.
The 20-year consent-order architecture is increasingly standard. Facebook's 2011 and 2019 consent orders, Marriott's 2024 consent order, and parallel structures across the FTC's recent enforcement actions all use 20-year compliance frameworks. The implication for PE sponsors and strategic acquirers is that consent-order obligations may exceed typical hold periods and must be evaluated as inherited liability in M&A.
What this means for boards and executives
The composite analysis points to four operational priorities. First, threat-hunting capability must be baseline, not premium. Second, M&A diligence must include forensic threat hunting for any consumer-data-rich target. Third, board-level cybersecurity governance — quarterly reporting, board cybersecurity expertise, documented oversight — is no longer aspirational but is increasingly treated as the baseline regulatory expectation under FTC consent orders and developing Caremark-doctrine case law. Fourth, incident-response playbooks must account for the SEC's four-business-day materiality determination clock and for the named-officer certification framework that has become standard in major enforcement actions.
Frequently asked questions
What was the biggest data breach in history?
By record count, the 2013 Yahoo breach affecting 3 billion accounts is the largest data breach in history. By financial penalty, the $5 billion FTC settlement with Facebook over Cambridge Analytica is the largest consumer-protection enforcement action. By number of affected organizations, the 2020 SolarWinds compromise notified approximately 18,000 organizations. The right answer depends on which dimension matters most for the question.
What was the most expensive data breach?
Equifax 2017 produced over $1.4 billion in direct costs across regulatory penalties, civil settlements, and remediation. Facebook-Cambridge Analytica produced approximately $5.7 billion across the FTC settlement, SEC penalty, class action, and U.K. ICO fine. Yahoo's $500 million-plus direct cost was smaller in absolute terms but produced larger regulatory precedent.
Which data breaches were caused by state-sponsored actors?
State-sponsored attribution in this ranking includes Yahoo (Russian FSB), Marriott-Starwood (Chinese MSS), SolarWinds (Russian SVR), Anthem (Chinese), OPM (Chinese), Microsoft Exchange ProxyLogon (Chinese HAFNIUM), and Bybit (North Korean Lazarus Group). Several others have suspected state-sponsored involvement that has not been formally attributed.
How long did attackers stay in networks before detection?
Detection delays varied substantially. SolarWinds: approximately 14 months. Marriott-Starwood: approximately 4 years. Yahoo: 2-3 years. Anthem: approximately 9 months. OPM: approximately 18 months. The pattern across major state-sponsored breaches is that 12-48 month dwell times are standard, not exceptional.
What is the M&A inheritance pattern in data breaches?
The Marriott-Starwood case is the canonical example. Chinese attackers were inside Starwood's reservation database for two years before Marriott's $13.6 billion acquisition closed and for two more years after. The acquirer inherited the active breach. The October 2024 FTC consent order codifies the regulatory expectation that acquirers conduct active forensic threat hunting before closing M&A transactions in consumer-data-rich sectors. Read more about cyber due diligence.
What is the SEC's four-business-day disclosure rule?
The SEC Cybersecurity Disclosure Rules effective in late 2023 require public companies to disclose material cybersecurity incidents in Form 8-K within four business days of materiality determination. The four-business-day clock derives substantially from the Yahoo SEC enforcement action's analytical framework. The October 2023 SEC enforcement against SolarWinds and CISO Timothy Brown was the first personal-liability action against a sitting CISO under the framework.
How does this ranking compare to other lists?
Lists that rank by record count alone elevate the LinkedIn 2021 scrape (700M), MySpace 2008 (360M), and Adult Friend Finder 2016 (412M) to top positions despite their relatively smaller regulatory and strategic consequence. Lists that rank by financial impact alone elevate Facebook-Cambridge Analytica ($5.7B) and Equifax ($1.4B+) above breaches with larger record counts. The composite-impact approach used here is intended to be more useful for executives, boards, and PE sponsors evaluating the breaches that matter most for governance and diligence practice.
<p>The right way to think about these 30 breaches is not as historical curiosities but as the empirical record that built modern cybersecurity governance. Every SEC Cybersecurity Disclosure Rule, every state attorney general settlement, every FTC consent order, every PE diligence playbook, every board cybersecurity reporting cadence inherits substantially from this record. The breaches that matter most are not necessarily the largest by record count; they are the ones that produced durable institutional consequence. The list above is anchored against the deeper analyses in the Cloudskope Breach Library, which examines each incident's executive implications, PE-relevant findings, and regulatory precedent in detail.</p>
.png)

.png)
.png)
