Russia Harvested 18,000+ Microsoft 365 Tokens Without Installing a Single File. Your Router Was the Weapon.
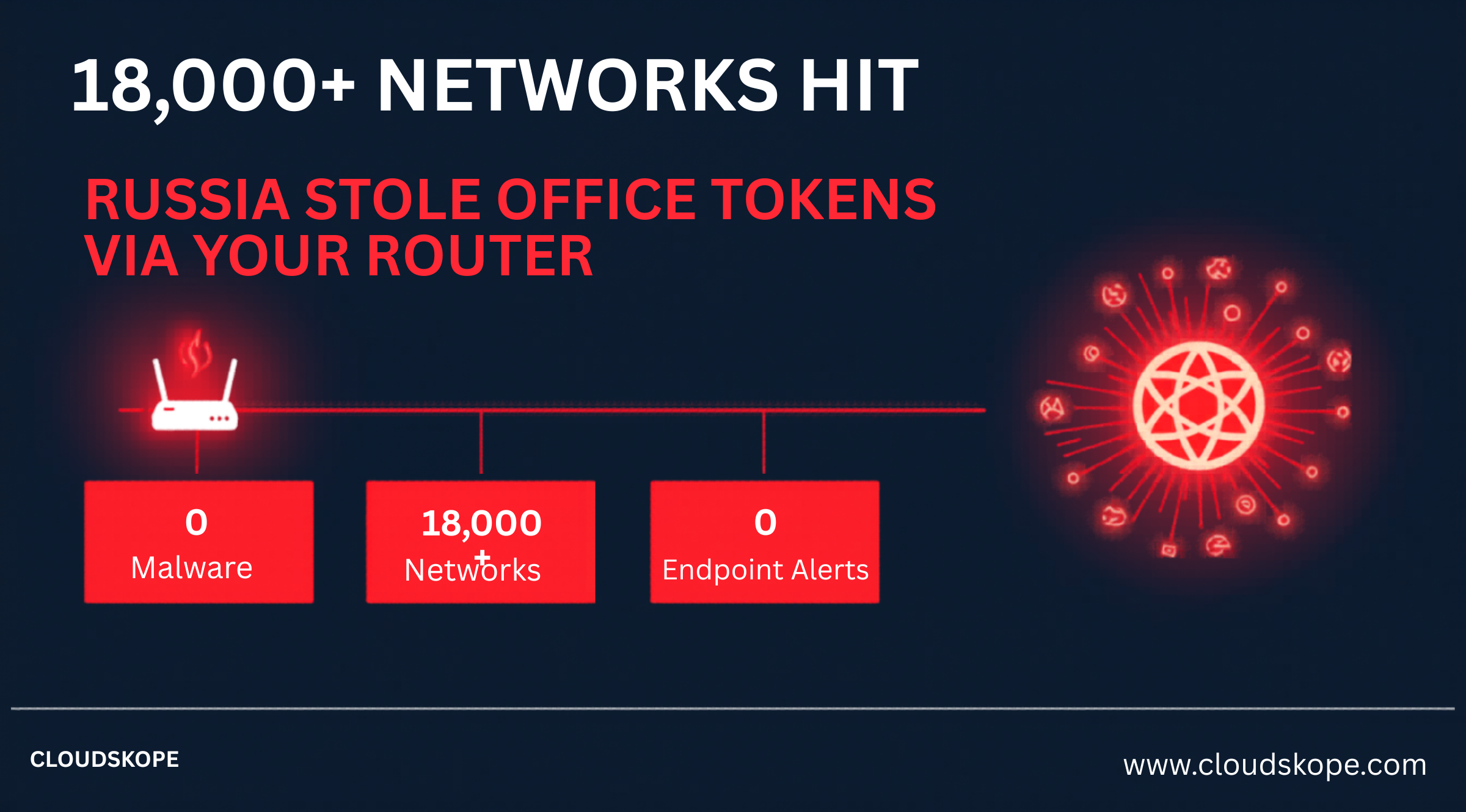
Security teams spent 2024 deploying endpoint detection agents, tuning SIEM rules, and hardening identity policies. Russian military intelligence exploited the one asset class that security budgets consistently underprioritize: the network infrastructure sitting between your users and the internet. Every endpoint detection platform on the market missed this campaign entirely. There was nothing on the endpoints to detect.
How the GRU Harvested Microsoft 365 Tokens at Scale
The campaign, attributed to GRU unit 26165 (also known as Fancy Bear, APT28, and Forest Blizzard), was disclosed by intelligence agencies and Microsoft in April 2026. Its technical mechanism is sophisticated in its choice of target — and trivial in its execution once that target is compromised.
Phase 1: Router Compromise
The GRU exploited known vulnerabilities in internet-facing routers — specifically older firmware versions in devices from Cisco, Juniper, MikroTik, and Ubiquiti that organizations had not patched. These are not zero-day exploits. They are published CVEs with available patches that IT teams deprioritized because router firmware updates are operationally disruptive and often require maintenance windows.
Once inside a router, the GRU did not install malware or modify configuration files visibly. They implanted a passive network listener — a configuration change that captured specific traffic types passing through the device. The listener targeted NTLM authentication handshakes in network traffic.
Phase 2: NTLM Token Harvesting
NTLM (NT LAN Manager) is a Microsoft authentication protocol that has been deprecated for nearly a decade but remains enabled by default in most Windows environments for backwards compatibility. When a Windows system authenticates to a network resource using NTLM, it exchanges a challenge-response handshake that contains the Net-NTLMv2 hash of the user's credentials. This handshake is transmitted across the network — and many internal protocols expose NTLM traffic to network-layer inspection. The GRU's router-based listeners captured these NTLM handshakes as they transited the compromised routers.
Captured Net-NTLMv2 hashes can be cracked offline using GPU-accelerated brute force. For accounts with weak or moderate passwords, cracking takes seconds to minutes. For Microsoft 365 accounts, the credential can then be used directly for authentication — bypassing endpoint detection entirely because the authentication originates from GRU-controlled infrastructure using legitimately obtained credentials.
Phase 3: Microsoft 365 Access
With cracked NTLM credentials in hand, the GRU authenticated directly to Microsoft 365 services. From Microsoft's identity systems, these logins appeared as credential-based authentications from unfamiliar IP addresses — unusual, but not inherently indicative of compromise without sophisticated Conditional Access analysis. Most mid-market Microsoft 365 tenants do not have Conditional Access policies restrictive enough to block authentication from unfamiliar IP ranges. The result: GRU-controlled actors had authenticated access to Microsoft 365 environments across more than 18,000 networks. Email, OneDrive, Teams, SharePoint — the full Microsoft 365 suite, accessible without touching a single endpoint.
The 18,000-network GRU campaign did not exploit Microsoft. It exploited the assumption that network infrastructure is outside the threat model. Every unpatched router is a passive listening post waiting for a nation-state to activate it.
Why NTLM Is Still Active in 2026
Microsoft has attempted to deprecate NTLM authentication for years. The challenge is backwards compatibility. NTLM is embedded in decades of Windows networking behavior — file share authentication, printer discovery, domain trust relationships, and legacy application authentication designed before Kerberos became the preferred protocol. Disabling NTLM outright breaks things. Often important things. Applications that authenticate using NTLM stop working. Printers using NTLM for spooler access stop printing. The operational disruption of NTLM disablement is sufficiently significant that most IT teams defer it indefinitely rather than undertake the remediation required to identify and replace all NTLM-dependent services.
The GRU understood this perfectly. NTLM is a legacy protocol that is too embedded to be quickly removed and too fundamental to be monitored with the scrutiny applied to newer authentication paths. It is the authentication equivalent of a side door that security teams know exists but have never gotten around to locking.
The Router Problem Is Structural
The deeper issue this campaign exposes is the unmanaged attack surface represented by network infrastructure. Routers, switches, firewalls, and load balancers are computers running operating systems with exploitable vulnerabilities. They are systematically excluded from the vulnerability management programs that cover endpoints and servers. The reason is operational: firmware updates for network infrastructure require maintenance windows, often take devices offline temporarily, and have historically caused unpredictable configuration issues. IT and security teams rationally deprioritize network infrastructure patching because the operational cost is visible and immediate, while the security benefit feels abstract until an incident demonstrates it.
In most mid-market enterprise environments Cloudskope assesses, network infrastructure firmware is running versions that are 18 to 36 months behind current releases. The CVEs exploited in this GRU campaign were published and patchable months before the campaign began.
The M&A Due Diligence Dimension
For private equity sponsors, this campaign has a specific implication: when you acquire a company, you inherit their router firmware debt. The GRU was harvesting tokens from 18,000+ networks simultaneously. Statistically, some of those networks belong to companies that are current or future acquisition targets. M&A cyber due diligence programs that focus exclusively on endpoint security, identity configuration, and data classification while ignoring network infrastructure firmware have a systematic blind spot that nation-state actors have already exploited at scale.
What Organizations Need to Do
The immediate action item for organizations that have not audited their router firmware in the past six months is to do so now. This means identifying every internet-facing network device, checking the current firmware version against available releases, and scheduling updates for devices running versions that contain known exploited vulnerabilities.
For Microsoft 365 environments, the specific control that limits the blast radius of NTLM token harvesting is Entra ID's ability to block legacy authentication protocols. Microsoft provides a Legacy Authentication Blocking Conditional Access policy template that, when properly configured, prevents authentication attempts using legacy protocols including NTLM relay through modern authentication endpoints. Combined with continuous access evaluation and device compliance requirements, this significantly reduces the usefulness of harvested credentials even if network capture occurs.
The harder structural change is treating network infrastructure as part of the vulnerability management program rather than a separate operational domain. This means router and firewall firmware versions appearing in vulnerability scan results alongside server OS patches, with defined SLAs for update deployment that match the severity of the CVEs involved. For PE sponsors conducting due diligence, network infrastructure firmware audit should be a standard component of technical diligence alongside endpoint coverage, identity configuration, and data classification.
The GRU harvested 18,000 networks without touching an endpoint. The implications for organizations that have built their entire security program on endpoint detection are uncomfortable: the network infrastructure you have not been auditing has been the attack surface all along. The router sitting between your users and the internet is not background infrastructure. In 2026, it is a target.
Cloudskope's Network and Infrastructure Security Assessment audits your edge infrastructure firmware, identifies NTLM exposure paths, and evaluates your Microsoft 365 Conditional Access posture against this specific attack class. For PE sponsors, our M&A Cyber Due Diligence program includes network infrastructure assessment as a standard component of pre-close technical review.
.png)




.png)
