April's 167 CVEs Were Not a Patch Problem. They Were a Governance Failure.
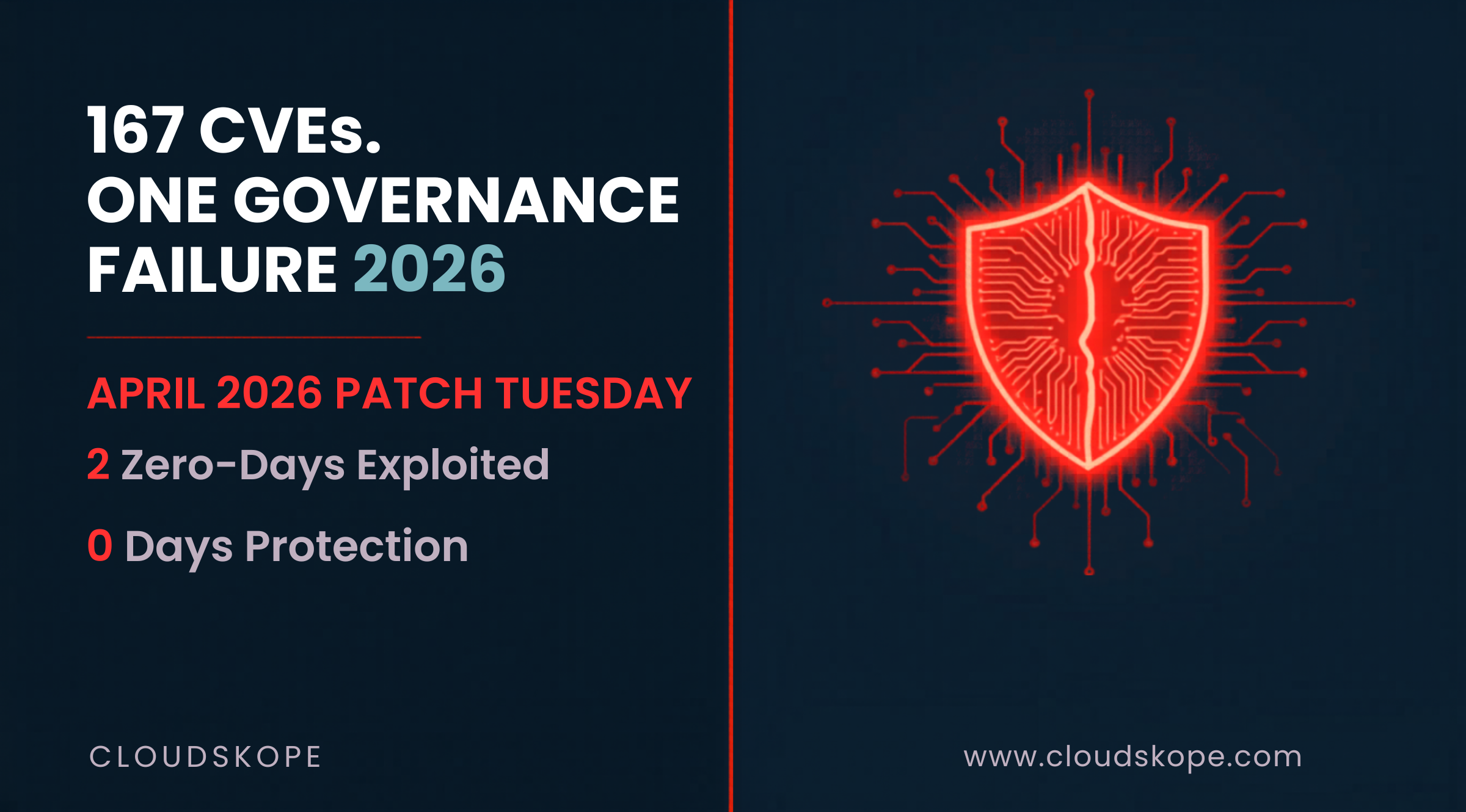
One hundred and sixty-seven vulnerabilities. In one month. From one vendor. If your board is not asking about patch velocity by name, your governance structure has a gap that no compliance framework is closing. April 2026's Patch Tuesday was not unusually severe — it was unusually visible. The number of CVEs addressed this cycle was not an anomaly. It was confirmation that 167 vulnerabilities per month is the new operating baseline for any organization running Microsoft infrastructure.
What April's Patch Tuesday Actually Disclosed
Microsoft addressed 167 security vulnerabilities in April 2026 — a number that will appear briefly in security newsletters before being buried under the next news cycle. That burial is itself a governance failure.
CVE-2026-32201: SharePoint Server Zero-Day
Microsoft confirmed that CVE-2026-32201 is being actively exploited in the wild. This is a content spoofing and interface falsification vulnerability in SharePoint Server that allows attackers to impersonate trusted content or interfaces over a network. SharePoint is not a peripheral application — it is the document backbone of virtually every mid-market Microsoft 365 deployment. A vulnerability that allows an attacker to present falsified SharePoint content to employees or partners is not a technical flaw. It is a social engineering amplifier. An attacker who can make a fraudulent SharePoint document look like an authentic executive communication has a phishing vector that bypasses every email gateway you own.
The attack path is straightforward: exploit CVE-2026-32201 to spoof a SharePoint notification, direct targets to a credential-harvesting page that looks exactly like a legitimate SharePoint login prompt, capture credentials. Your SIEM will see an authenticated login. Your EDR will see nothing. Your email security gateway will see nothing, because the attack never came through email.
CVE-2026-33825: BlueHammer — Windows Defender Zero-Day
BlueHammer is a privilege escalation vulnerability in Windows Defender itself — the security tool you deployed specifically to stop privilege escalation. The researcher who discovered BlueHammer published working exploit code publicly before Microsoft's patch was available. For a window of time, every organization running Windows Defender had a publicly documented, working privilege escalation path that any attacker could execute. Defender runs as SYSTEM. A privilege escalation flaw in Defender is functionally a direct path to SYSTEM access on any Windows endpoint — which is most of them.
Office Preview Pane RCEs and Chrome Zero-Days
This cycle addressed multiple Microsoft Office remote code execution vulnerabilities that can be triggered simply by previewing a booby-trapped message in Outlook's preview pane — no click required, no macro execution, no user action beyond opening email. Additionally, Google Chrome received its fourth zero-day patch of 2026, and Adobe Reader required an emergency patch for an actively exploited remote code execution flaw. Four Chrome zero-days in four months means the browser is now the primary attack surface for enterprise endpoints, and patching cycles that run on 30-day IT schedules are structurally incompatible with zero-day exploitation timelines measured in hours.
BlueHammer is not a Defender flaw — it is proof that every security tool in your stack is simultaneously a control and an attack surface, and most organizations have no plan for the second scenario.
Why 167 CVEs Is Not a Crisis — It Is the New Normal
Microsoft has consistently released 100-plus CVEs per Patch Tuesday for the past 24 months. The volume has plateaued at a level that most organizations' patch management programs were not designed to handle. Traditional patch management was built on a model where patches were applied monthly by IT, tested for compatibility over two to three weeks, and deployed in a maintenance window. That model assumes a monthly patch cycle is faster than the exploitation timeline for newly disclosed vulnerabilities. That assumption has not been true since 2021, and it is catastrophically false in 2026.
Nation-state threat actors weaponize high-severity Microsoft vulnerabilities within 24 to 72 hours of disclosure. Criminal ransomware groups follow within days. The SharePoint zero-day in this cycle was already being exploited before Microsoft disclosed it.
The Governance Dimension That Boards Are Missing
Patch velocity has crossed from an IT operational metric into a board-level governance indicator. The SEC's cyber disclosure rules require boards to maintain adequate risk oversight. The FTC has pursued enforcement actions against organizations whose breach investigations revealed knowingly unpatched systems. The EU's NIS2 Directive includes patch management as an explicit governance requirement for covered entities.
Cyber insurance carriers are increasingly requiring organizations to demonstrate patch deployment SLAs that meet defined timelines for critical and high-severity vulnerabilities. Organizations that cannot demonstrate a 14-day SLA for critical patches are losing coverage or facing exclusions. Organizations that cannot demonstrate a 72-hour SLA for actively exploited zero-days are increasingly uninsurable at preferred rates. If your board does not currently receive a monthly metric showing mean time to patch for critical vulnerabilities alongside your financial reporting, you have a governance gap that is now measurable in insurance premium dollars.
What This Means for Private Equity Portfolio Companies
For PE sponsors and operating partners, April's Patch Tuesday has a specific implication that general cybersecurity coverage will not surface: patch velocity is now a material variable in deal valuation and post-close operating risk. When a portfolio company is acquired with a known critical vulnerability unpatched — particularly CVE-2026-32201, which enables credential theft at scale — the acquirer inherits exposure that may have already been exploited before the deal closed. In M&A due diligence, patch velocity and vulnerability management program maturity should be evaluated alongside financial controls. A target company whose IT team cannot demonstrate a defined SLA for critical patch deployment has an operational risk that belongs in the deal model, not the post-close 100-day plan.
The Executive Action Items From This Cycle
For organizations running SharePoint Server on-premises or in hybrid configurations, CVE-2026-32201 requires immediate prioritization. Microsoft has released the patch. For Windows Defender deployments, BlueHammer requires the same urgency. The existence of a public proof-of-concept means the exploitation bar is now near zero for any attacker with basic tooling. More broadly, this cycle should prompt every organization to review whether their patch management SLA is documented, enforced, and measured — not described in a policy document, but actually measured, with exception reporting that reaches senior leadership when SLAs are missed.
April's 167 CVEs are not a Microsoft problem. They are a governance problem that happens to manifest through Microsoft software. The organizations that treat Patch Tuesday as an IT task will continue to be the case studies that fill next year's breach reports. The ones that treat it as a governance metric will be the ones explaining to their boards why they didn't make the news.
Cloudskope's Cyber Risk Assessment benchmarks your patch velocity, vulnerability management SLAs, and exception handling processes against what attackers actually exploit. For PE sponsors, our M&A Cyber & IT Due Diligence program evaluates target company patch posture before deal close, giving you a documented risk position rather than an inherited surprise.
.png)
.png)

.png)