Audited. Compliant. Hacked Anyway.
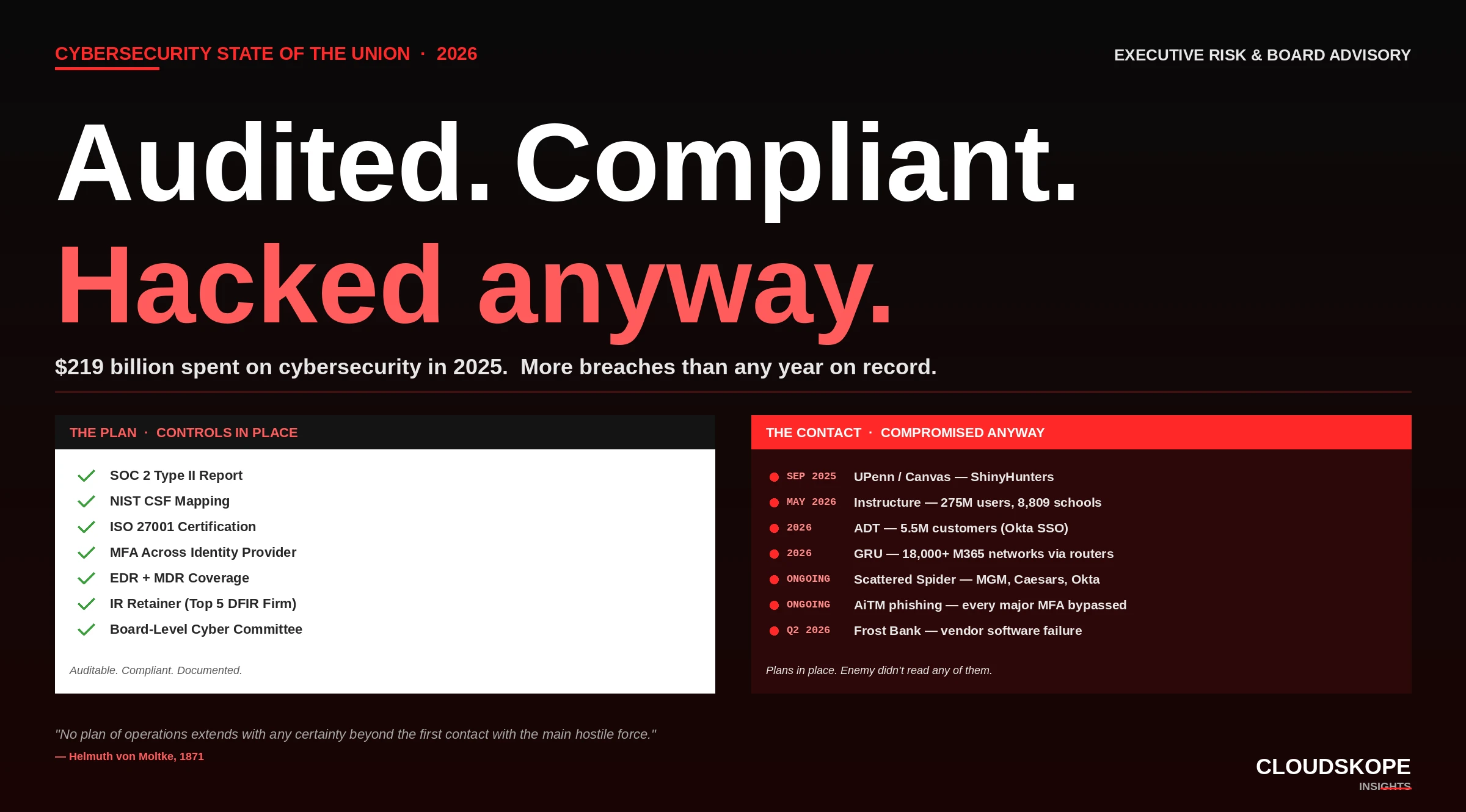
There is an old line from Prussian field marshal Helmuth von Moltke: "No plan of operations extends with any certainty beyond the first contact with the main hostile force." Cybersecurity, in 2026, has become a $219 billion industry of plans that do not survive contact with the enemy.
When the Plans Stop Working
In 1871, after Prussia had defeated France and the German Empire was being formed, Field Marshal Helmuth von Moltke wrote down the lesson he believed every general would have to learn. The full quote, not the version that gets repeated in business-school case studies, reads: "No plan of operations extends with any certainty beyond the first contact with the main hostile force."
Moltke wasn't saying plans were useless. He was saying something more uncomfortable. He was saying that the act of planning, however thorough and however well-resourced, has a hard limit — and that limit is the first moment the plan meets reality. After that moment, the plan ceases to be a guide. It becomes a record of what someone thought might happen.
In 2025, the global cybersecurity industry spent approximately $219 billion. Most of that spending paid for plans.
It paid for incident response plans, for vendor risk assessments, for tabletop exercises, for compliance audits, for SOC 2 Type II reports, for NIST Cybersecurity Framework mappings, for ISO 27001 certifications, for MITRE ATT&CK matrices on PowerPoint slides. It paid for runbooks no one reads, for retainers with incident response firms no one has called, for cyber insurance policies that pay out under conditions no one can meet, and for board reports that translate the actual security posture of the organization into a green-yellow-red traffic light.
The same year produced more major breaches than any in recorded history. The plans were in place. The enemy did not read any of them.
The Plans That Were Already in Place
It is easy to look at the 2026 cybersecurity landscape and conclude that the organizations getting compromised were unprepared. The opposite is true. They were extensively prepared. They had plans.
When ShinyHunters compromised the University of Pennsylvania through Canvas in September 2025, Penn had a documented vendor risk management program, an annual SOC 2 review of major SaaS partners, an incident response retainer with a top-five DFIR firm, and a board-level cyber governance committee. The Penn breach happened anyway.
When ShinyHunters re-compromised Instructure in May 2026, eight months after Penn, Instructure had a CISO, a documented incident response plan, an active Statuspage subscription, and external counsel on retainer for breach notification. The recompromise happened anyway — and the public response was a "scheduled maintenance" page that ran twenty-one minutes ahead of the actual acknowledgment.
When ADT lost data on 5.5 million customers through Okta SSO and Salesforce in early 2026, ADT was a security company. It sold home security. It ran a security operations center. It had MFA on Okta. It had Salesforce DLP. It had been audited. The breach happened anyway.
When the GRU harvested Microsoft 365 authentication tokens from more than 18,000 networks, those networks had endpoint detection. They had patch management programs. They had identity governance policies. The harvest happened anyway — because the attack surface was not their endpoints, their identity provider, or their vendors. It was their routers. Routers do not appear in any of the plans.
The pattern is structural. These organizations were not casual about security. They had bought, deployed, audited, and reported on substantial defensive postures. And the postures did not survive contact with the actual enemy.
Moltke did not say plans were useless. He said they did not survive contact. The cybersecurity industry has not yet learned the difference between those two claims.
Why the Plans Keep Failing
The cybersecurity industry has produced a generation of plans optimized for everything except the moment the plan needs to work. Six structural reasons.
- Plans are written for the audit, not the attack. SOC 2 Type II, ISO 27001, NIST CSF, HIPAA, FedRAMP — these frameworks define what evidence an organization can produce on demand to a third party. They are designed for review, not response. An incident response plan that satisfies a SOC 2 auditor is not the same artifact as an incident response plan that survives a Thursday afternoon recompromise during finals week. The first is a document. The second is a muscle memory. Most organizations have the first.
- Plans assume the attacker plays by the rules the plan defines. A plan that addresses ransomware does not address pure data extortion. A plan that addresses endpoint compromise does not address router-level credential harvesting. A plan that addresses external attackers does not address an Okta admin who was phished while on vacation. The threat models embedded in most plans are 18 to 36 months behind the threat models the actual adversaries are operating with.
- Plans assume time. Most incident response plans assume the organization will have time to consult counsel, convene the crisis team, and notify the right stakeholders in the right order. In practice, contact with the enemy collapses that time horizon. Instructure had between roughly 3:30 PM Eastern and 4:20 PM Eastern on May 7, 2026 to make the decision that ended up defining its incident communications. Fifty minutes. That is not enough time to follow a written process. That is enough time only for reflex.
- Plans assume the help desk is not the vulnerability. Most plans designate help desks as support infrastructure rather than as adversary entry points. Scattered Spider demonstrated, repeatedly, that this assumption is wrong. The MGM breach, the Caesars breach, the Okta breach — each involved a help desk performing exactly the action the help desk was designed to perform, on behalf of an attacker who had researched the victim. The plan said the help desk follows verification procedures. The verification procedures were never designed to resist social engineering. The plan didn't account for the procedures being the vulnerability.
- Plans assume people who follow procedures. They do not account for the most senior people in an organization actively choosing to ignore the procedures because the optics are inconvenient. Instructure's "scheduled maintenance" framing on May 7 was not a procedural failure. It was a choice. The plan said the procedure was "communicate transparently with affected customers." The choice was "communicate the framing most favorable to the brand." The plan did not anticipate that the procedure would be overruled at the moment of contact.
- Plans assume the threat model the plan was built for. They do not account for the threat model that exists in 2026, which has moved decisively to identity, supply chain, vendor concentration, and trust collapse. Plans written for the malware era are still being audited as if they were the relevant defensive posture. They are not. The malware era ended somewhere between 2020 and 2022. Most plans have not caught up.
What Contact With the Enemy Actually Looks Like
Strip away the abstractions. The plans fail because the moments they have to survive do not look like the moments they were written to address.
Contact with the enemy in 2026 is a CFO whose voice is cloned from a public podcast appearance, calling the help desk from an unknown number, talking about a personal emergency, requesting an MFA reset — and receiving it. There is no plan in that scenario. There is only what the help desk agent does in the fifteen seconds between the request and the action. That fifteen seconds is the entire defensive posture of the organization.
Contact with the enemy is an Okta administrator, on vacation, who clicked a calendar invite, then a "verify your session" prompt, then approved an MFA push notification because the prompt was timed to a session he had just initiated. Forty minutes later, that administrator's privileged access was used to enroll a new device, which was used to access Salesforce, which was used to extract 5.5 million customer records. No plan addresses that exact sequence.
Contact with the enemy is a Free-For-Teacher account, created in 2014, on a Canvas instance that grew to host 9,000 institutions, which never received the architectural review it would have needed because it predates the modern Canvas security program by a decade. The plan assumed the security boundary was between Canvas tenants. The actual security boundary was between Free-For-Teacher accounts and paid institutional accounts. The plan addressed the wrong boundary.
Contact with the enemy is a router running firmware released eighteen months ago, sitting on a corporate network where the IT team has consistently deprioritized firmware updates because the operational disruption is visible and immediate while the security benefit feels abstract. The plan said routers were managed. The plan did not say which version they were on, when they were last updated, or what would happen if Russian GRU operators implanted a passive NTLM listener.
None of these scenarios are exotic. All of them happened in the past twelve months. All of them happened to organizations with plans.
The Moltke Alternative
What Moltke Actually Said Next
The Moltke quote is usually shortened, in business contexts, to "no plan survives contact with the enemy." That truncation removes the actual lesson. Moltke's full argument continued: "Therefore strategy is a system of expedients. It is more than a science. It is the application of knowledge to practical life, the development of an original idea in accordance with continually changing circumstances. It is the art of acting under the pressure of the most difficult conditions."
Moltke was not arguing against planning. He was arguing for something much harder: that the people who would have to act, at the moment of contact, must be trained for improvisation under fire — and that this training is not the same as preparation through plans. Plans produce documents. Improvisation under fire produces capability. The two are not interchangeable.
The cybersecurity industry has produced an enormous quantity of plans. It has not produced anywhere near enough capability.
The State of the Union
In 2026, the global cybersecurity industry's largest annual budget line items are not defensive. They are documentary. The largest spending categories are compliance audits, vendor risk reviews, governance reporting, framework certifications, and the consulting industry that supports them. The smallest categories — relative to spending — are the things that actually develop capability: red team exercises modeled on the actual adversaries currently operating in the wild; tabletop exercises that explicitly remove the planning artifacts from the table and force decision-making under time pressure; help desk vishing simulations conducted by people who can pass for the real attackers; and post-incident debriefs that name the specific person who made the specific decision and what they would do differently.
The industry has financialized planning. It has not financialized readiness.
This is the structural problem. It is not a problem of attention — CISOs talk about readiness constantly. It is not a problem of budget — cybersecurity budgets have grown for fifteen consecutive years. It is a problem of incentive: the audit produces a document the board can act on, the vendor produces a report the auditor can verify, the framework produces a certification the customer can require — and none of these incentive loops terminate at "the moment the help desk agent decides whether to reset the MFA." That moment is where contact with the enemy happens. That moment is also where the industry, structurally, has not invested.
What Has to Change
Six things, in rough order of leverage.
- Stop confusing certification with capability. SOC 2, ISO 27001, NIST CSF, HIPAA — these are necessary, but they are entry tickets, not finish lines. An organization that treats its certification posture as evidence of defensive capability has already lost the argument. Boards should require both certification and capability evidence, and they should be different evidence.
- Run drills that explicitly remove the plan from the table. Tabletop exercises that involve a printed playbook test the playbook. They do not test the people. The drills that matter are the ones where the playbook is unavailable, the senior leader is unreachable, the news cycle is moving in real time, and the decision must be made in the next ninety seconds. Most organizations have never run that drill.
- Treat the help desk as a critical security function. Not as an extension of IT. Not as a support team. As a frontline defensive function with the threat model, training, escalation paths, and authority equivalent to a security operations center. Most organizations resource their help desk at one-twentieth of what they resource their SOC. The adversary has noticed.
- Audit the assumptions baked into the threat model, not just the controls. A vendor risk program that audits SOC 2 reports without auditing the actual access paths through the vendor's infrastructure is auditing controls without auditing assumptions. The Canvas / Penn / Instructure sequence shows what happens when assumptions about tenant separation, federated identity, and free-tier accounts go unexamined. Most vendor risk programs do not examine them.
- Develop in-house adversary fluency. Most security teams know their tools better than they know the adversaries currently targeting their sector. That is backwards. The adversary fluency required in 2026 is specific: who is operating against your sector, what their access patterns are, what their first ninety seconds inside an environment look like, and what they typically ask for. Most security teams could not answer those four questions for any of the three adversary groups currently most active against them. Most CISOs could not either.
- Build organizational memory of contact with the enemy. The most useful artifact any security team can produce is the unredacted, signed-by-name account of what happened during the last incident, including the specific decisions made under time pressure, the specific framings used in communications, and the specific things that would be done differently. Most organizations either do not produce this artifact or restrict it so heavily that it provides no learning value. The institutional knowledge that survives contact with the enemy is the knowledge that gets written down, attributed to specific people, and read by the people who would have to make the same decisions next time.
The cybersecurity industry has had every advantage in the past five years: more spending, more talent, more frameworks, more vendor capability, and more public visibility into adversaries than ever before. It has also had the worst five years of breach activity in recorded history. Those two facts are not in tension. They are causally related. Moltke did not say plans were useless. He said they did not survive contact. The cybersecurity industry has not yet learned the difference. The organizations that will be defensible in 2030 are not the ones with the most certifications today. They are the ones training their people for the moment the plans stop working. The enemy has read all of this before. He just hasn't read your plan.
Cloudskope helps mid-market enterprises, PE-portfolio companies, and education and healthcare institutions develop the operational readiness that compliance frameworks alone cannot produce. We design and run unscripted incident drills, conduct help desk vishing simulations, and pressure-test vendor risk assumptions against the threat models currently in active use. Our M&A Cyber Due Diligence and Executive Risk Advisory programs surface the specific contact-with-the-enemy capability gaps that boards need to address before the next compromise.
.png)



.png)

.png)