Security Blog
Expert insights, threat intelligence, and best practices from our security team
30 Biggest Data Breaches of All Time: A Ranked Analysis of Impact, Cost, and Regulatory Precedent
<p>A composite-impact ranking of the 30 most consequential data breaches in the public record, evaluated across record count, direct financial cost, regulatory enforcement, strategic intelligence significance, and the regulatory frameworks they catalyzed. Designed for executives, board directors, and PE sponsors who need an integrated reference to the breaches that shaped current cybersecurity governance, disclosure rules, and M&A diligence practice.</p>
Latest Articles
Most Common Passwords 2026: What the Data Shows and What Boards Should Do About It
<p>The 20 most commonly used passwords in 2026, analyzed from major breach corpora and credential-stuffing datasets, with discussion of why the list has been so stable for over a decade and what boards should be doing about authentication architecture in response.</p>
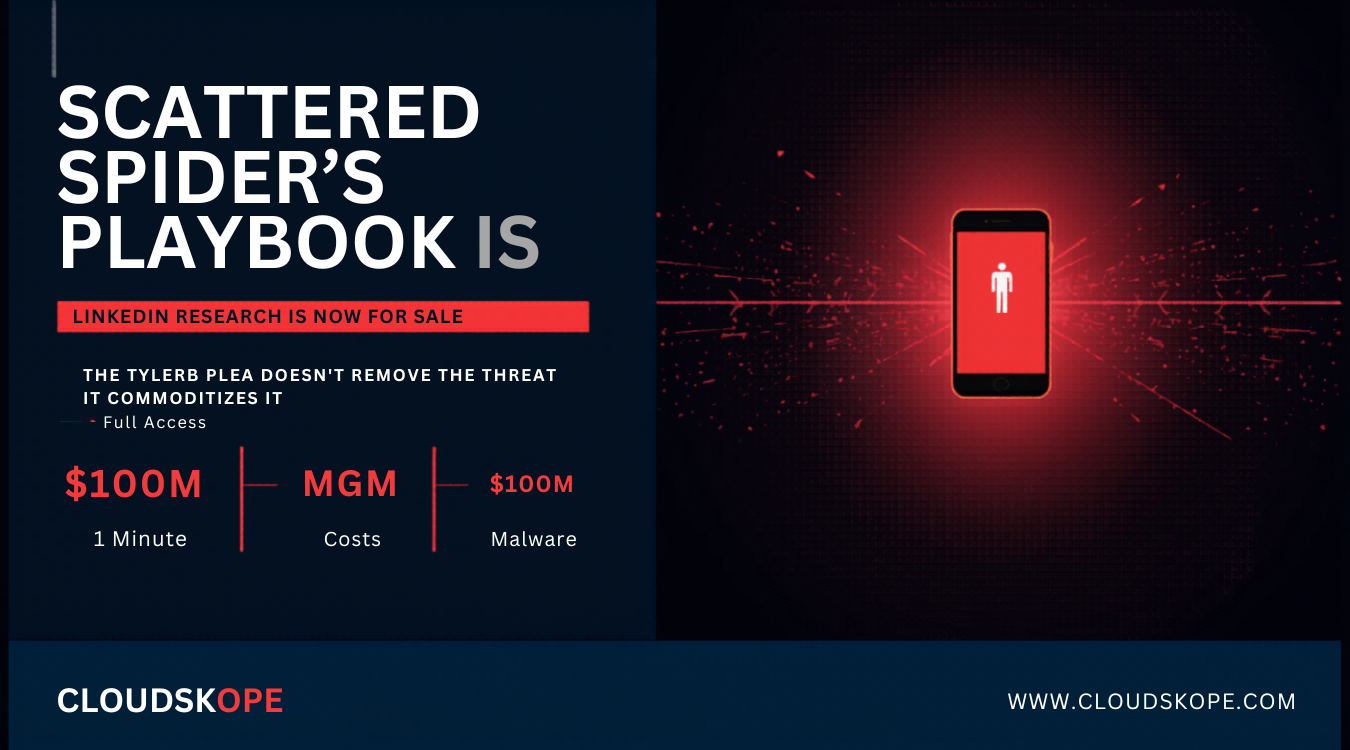
Scattered Spider Just Filed a Guilty Plea. The Real Threat Is That Their Playbook Is Now a Training Manual.
Tyler Buchanan, known as Tylerb, pleaded guilty in April 2026 to wire fraud conspiracy and identity theft as a senior member of Scattered Spider. The arrest and conviction will have no meaningful effect on the attack techniques Scattered Spider made famous, which have been replicated, documented, and sold across criminal markets since 2023.
Your Employees Are Running Shadow AI Agents With Admin Access to Everything. You Don't Know About Any of Them.
AI agents — autonomous programs that access email, Slack, Salesforce, SharePoint, and financial systems on behalf of users — are proliferating across enterprise environments without security review, inventory, or governance. Gartner named shadow AI agents the top emerging risk for CISOs in 2026. Google's security team warned they will create invisible, uncontrolled pipelines for sensitive data. Neither adequately described how bad this already is.
Every MFA Tool in Your Stack Is Being Bypassed Right Now. Here's Exactly How.
MFA deployment announcements still appear in board-level cybersecurity updates as evidence that an organization is protected. They are not. The five techniques now routinely used to defeat MFA have been operational for years — and most organizations that deployed MFA in 2020 still have no defenses against any of them.
We Tested Microsoft Defender, CrowdStrike Falcon, and SentinelOne Against the Same Attack. Here's What Actually Stopped It.
The MDR market generates billions of dollars annually on the premise that one platform detects threats better than another. In real engagements across mid-market enterprises, the platform matters far less than vendors want you to believe — and the team running it matters far more than most organizations are willing to pay for.
UniFi Dream Machine Beast: A Bold 2026 Push into Enterprise Gateways
The new UniFi Dream Machine Beast (UDM-Beast) just raised the bar on enterprise gateways. Full 2026 lineup comparison, specs, and honest head-to-head analysis vs Fortinet, Cisco, and Palo Alto. Price/performance, TCO, and when it actually wins for PE portfolios and mid-enterprise networks.
Microsoft 365 Copilot Does Not Create a Data Problem. It Reveals the One You Already Have.
Microsoft 365 Copilot is not just another productivity tool. It sits inside the operating layer of modern work: Outlook, Teams, SharePoint, OneDrive, Word, Excel, PowerPoint, and Microsoft Graph. That is why the risk is not theoretical. If your organization is using Microsoft 365, then Copilot is not entering a clean environment. It is entering years of permissions, legacy SharePoint sites, Teams channels, OneDrive links, stale groups, external sharing decisions, sensitive files, abandoned content, and access policies that may or may not still reflect business reality. The uncomfortable truth is simple: Copilot does not create your data governance problem. It reveals the one you already have.
The Uncomfortable Truth About AI Threat Detection: Why Your Security Stack is Actively Eroding M&A Deal Value
The cybersecurity industry is peddling a dangerous fantasy. Discover why your new "AI-powered" threat detection platform won't protect you from the autonomous Agentic AI workflows actively eroding your M&A deal multiples.
Flat Networks Turn Small Incidents Into Enterprise Events
When networks stay flat, small compromises escalate fast. This executive brief explains why segmentation, containment, and lateral-movement control now belong in board-level cyber risk discussions.
Ransomware Attack Trends: Q2 2026 Analysis
Q2 2026 ransomware trends show a shift toward targeted exploitation, data theft, operational disruption, and vendor exposure. Here is what executives should do now.
Your Network Gear Is Becoming the Attack Surface Nobody Audits Enough
Firewalls, SD-WAN controllers, VPNs, routers, and edge appliances are no longer background infrastructure. They are privileged control planes that must be governed, patched, monitored, and audited.
Patch Tuesday Is Not an IT Task. It Is a Governance Test.
Microsoft’s April 2026 security release reinforces a larger executive lesson: vulnerability management is not simply patch deployment. It is a test of asset visibility, ownership, prioritization, and business risk governance.
What Is SOC 2 Compliance? The Executive Guide to Trust, Controls, and Audit Readiness
Learn what SOC 2 compliance means, what a SOC 2 audit includes, SOC 2 Type 1 vs Type 2, Trust Services Criteria, controls, costs, checklist, and readiness steps.
When the Security Tool Becomes the Attack Surface: What the Microsoft Defender BlueHammer Zero-Day Should Teach Every Executive
Defender is a strong baseline, but it is still software. When the security tool itself is exploitable, organizations need layered controls that can contain execution, privilege escalation, credential access, and lateral movement even when one layer fails.
Cybersecurity Acronyms: A Complete 2026 Glossary for Executives, Boards, and Practitioners
<p>A complete glossary of the 70+ cybersecurity acronyms that matter most for executives, boards, audit committees, and PE sponsors in 2026 — organized across identity and access, detection and response, network security, cloud, application security, compliance, threat intelligence, cryptography, roles, vulnerability management, and email security.</p>
Cybersecurity Acronyms Glossary: 60+ Essential Terms Defined
A comprehensive glossary of the most important cybersecurity acronyms, organized by category and explained in operational context. Covers authentication and access (MFA, SSO, IAM, ZTNA), threats (APT, BEC, DDoS, MITM), defenses (EDR, XDR, MDR, SIEM, SOAR, WAF, DLP, CSPM), frameworks (NIST, SOC 2, HIPAA, GDPR, PCI DSS), cryptography (AES, RSA, TLS, PKI), and more.
Seven Years. Five Major Outages. Wells Fargo Still Calls It "Routine Maintenance."
A multi-year audit of Wells Fargo's outage history reveals a repeating pattern: power-related infrastructure failures, opaque communication, and prolonged customer impact framed as "routine maintenance." For boards and PE sponsors, the lesson is not that Wells Fargo has IT problems. It is that operational resilience is a structural cyber risk that shows up in patterns, not single events — and that vendor communication language is its own audit-grade signal of governance health.
Frost Bank and the New Vendor-Risk Reality
A vendor incident may begin outside your walls, but customers, regulators, and plaintiffs experience the outcome as your breach. Frost Bank is a timely reminder that third-party risk is now first-party accountability.
.png)

.png)
.png)